“Alexa, are you spying on me?” — aaaa…..mmmm…..hmmm…..maybe!!!
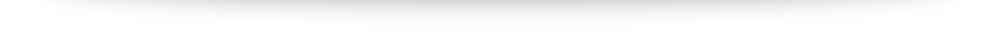
Security researchers have developed a new malicious ‘skill’ for Amazon’s popular voice assistant Alexa that can turn your Amazon Echo into a full-fledged spying device.
Amazon Echo is an always-listening voice-activated smart home speaker that allows you to get things done by using your voice, like playing music, setting alarms, and answering questions.
However, the device doesn’t remain activated all the time; instead, it sleeps until the user says, “Alexa,” and by default, it ends a session after some duration.
Source: Amazon Alexa Has Got Some Serious Skills—Spying On Users!
![]()