Botnets and DDoS attacks continue to grow in scale. Tackling them is no easy task, says a US government report.
Improving device security, better coordination between infrastructure companies, and smarter procurement by businesses are all part of tackling the botnet menace, according to a US government report.
The snappily titled Enhancing the Resilience of the Internet and Communications Ecosystem Against Botnets and Other Automated, Distributed Threats report is the result of an executive order signed by President Donald Trump last May aimed at strengthening the cyber security of federal networks and critical infrastructure.
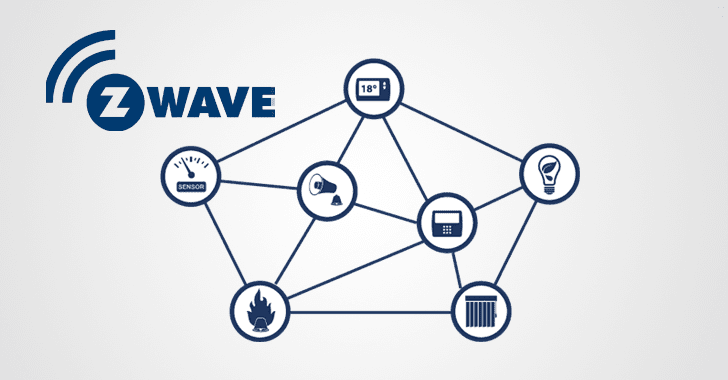
Botnets and the distributed denial of service (DDoS) attacks they deliver are a growing menace.
Source: Internet security: Slaying the botnet beast and the DDoS dragon | ZDNet
![]()